Controlhost.exe is found to be a vicious trojan horse infection that technically belongs to cryptominer or say trojan miner infection. This kind of infectious objects are mostly used to mine digital currency variants like Monero, Darnetcoin, Bitcoin, and many more. This kind of trojans are being widely used by malware authors these days. Once such traits are installed on a machine, it utilized internal computer resources like CPU or GPU to mine crypto currencies, however this leads to lack of resources for genuine applications and games while being used. Means, it simply indicates that Controlhost.exe can lead to severe damages inside computer and makes the PC access terrible for users in no time.
As noticed in most of the instances, the trojan miners like Controlhost.exe mostly spread over web through social networking platforms like Skype. It’s presented to users as a message in which the trojan is disguised, and when a user click those elements, the hidden trojan executes on compromised computers without any prior notice. Further, it manage to modify a number of critical settings, security applications, and more other traits, which makes the PC keeps crashing or freezing frequently. The victims are expected to see boot erros, BSOD errors, and more other scary messages on screen.
In addition to these, Controlhost.exe can also be installed on computer through other deceptive marketing gimmicks like Software Bundling, email spam marketing, and more. In order to prevent such things to intrude on a machine, the victims should be highly cautious against such intruders specially while surfing unsafe or unreliable online sources. While installing some freeware or shareware applications, a user might check Advanced/Custom installation mode to identify and deselect any unwanted apps. However, in case if your machine is currently infected, get through guidelines under this article to delete Controlhost.exe.
Threat Summary
Name: Controlhost.exe
Type: Trojan, coin miner, spyware
Description: Identified as a malicious trait or a vicious trojan horse infection, Controlhost.exe can be highly terrible for victims if remains untreated on computers for long time.
Distribution: Malicious links or ads, freeware or shareware installer packages, email attachments or links, and so on.
Removal: We suggest you checking through the guidelines under this article to identify and remove Controlhost.exe from compromised computers easily.
Special Offer (For Windows)
Controlhost.exe can re-install itself if its associated files remain on system somehow. We suggest users to try Spyhunter to check and clean their system against all malicious files completely.
For more information, read SpyHunter’s EULA, Threat Assessment Criteria, and Privacy Policy. Spyhunter checks that your computer has malware with its free trial version. If found any threat, it takes 48 hours time for its removal. If you need to eliminate Controlhost.exe instantly, you are required to purchase licensed version of this software.
As mentioned earlier, cyber-criminals have expertise to use some of the services offered by Windows System process as vulnerabilities. They usually mimic a legitimate system process with name of the Trojan or malware. They create the process of a Trojan same as some legitimate system process. In some cases, they easily get differentiated from legit processes however; some cases can be extremely difficult to distinguish.
If you examine the Windows process category in the Task Manager, you would easily notice the legitimate system process. However, if you notice duplicate files process, one must be a malware. This type of Trojan or malware continuously mines bitcoin or other crypto-currencies and this is a very high resource extensive process. The overall speed and performance of the PC gets extremely slow and sluggish. For depth enquiry, you can right click on the doubtful process and choose file location option in order to see the associated program. As a simple rule, if the file is stored in Windows/System32 folder, it is legitimate.
On the other hand, if the process is stored in the user’s processes or “Open the file” for the process leads to any random directories then it is doubtful. You should immediately scan your work-station with a powerful anti-malware tool. Remember that manual removal of harmful process related to Trojan or suspicious files are very difficult due to its deep intrusion and integration with the OS.
How to Remove Controlhost.exe
The first thing that you should do is to scan your work-station with a powerful anti-malware tool and that will be very helpful. On the other hand, if you have backup of your important data in any external clean location such as hard-drive or pen-drive etc. then formatting the infected hard-drive of the PC may also work for you. Remember that formatting the hard-drive may work for one PC but if the infected PC is connected with a network of PCs then this step will go in vain.
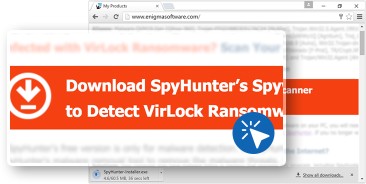
Click on the “Download” button to use “SpyHunter” anti-malware tool to clean your workstation.
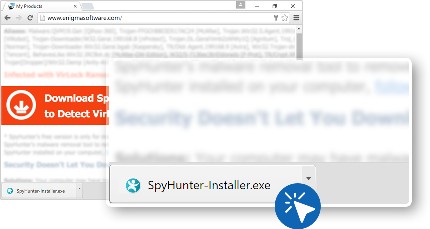
- On click on the download button, the file named as “Spyhunter-Intaller.exe” gets downloaded.
- In the downloads dialog box, choose “SpyHunter Installer.exe” and open the file.
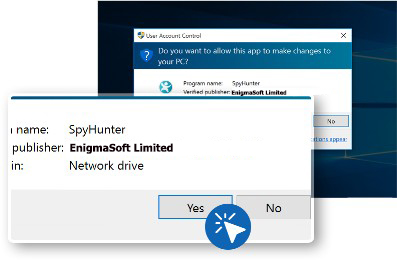
- Select “Yes” in the “User Account Control” dialog box.
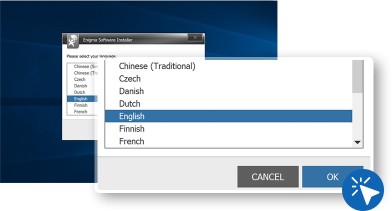
- Select the language you prefer and press on “OK” to get next step
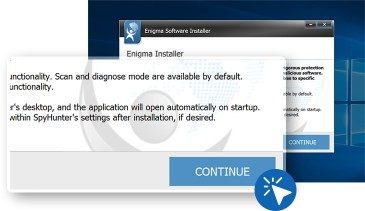
- In order to process the installation, press on “Continue”
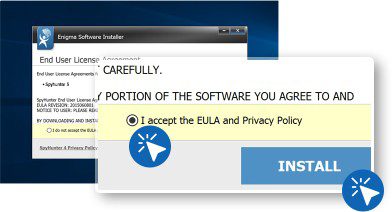
- Accept the privacy policy and end user agreement.
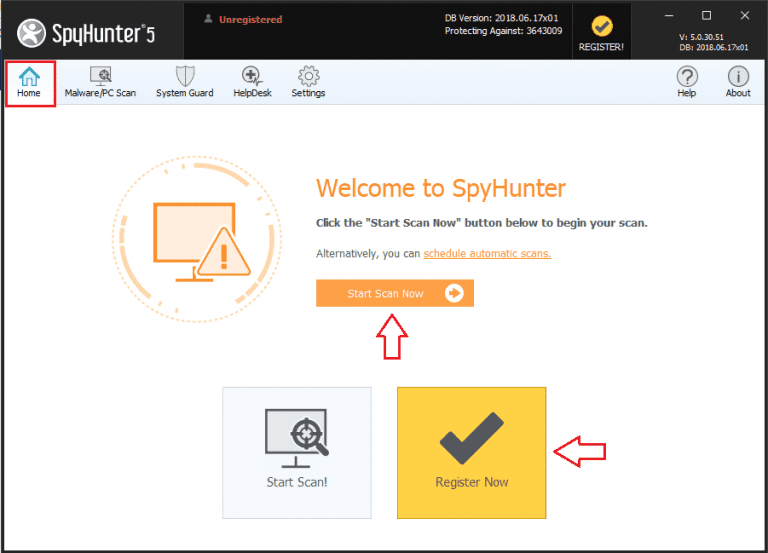
- Open “SpyHunter” by locating its icon on the desktop or search it on Windows “Start” menu.
The next step is to use “SpyHunter” for PC scanning and malware removal.
- Go to the “Home tab” and press on “Start Scan” button
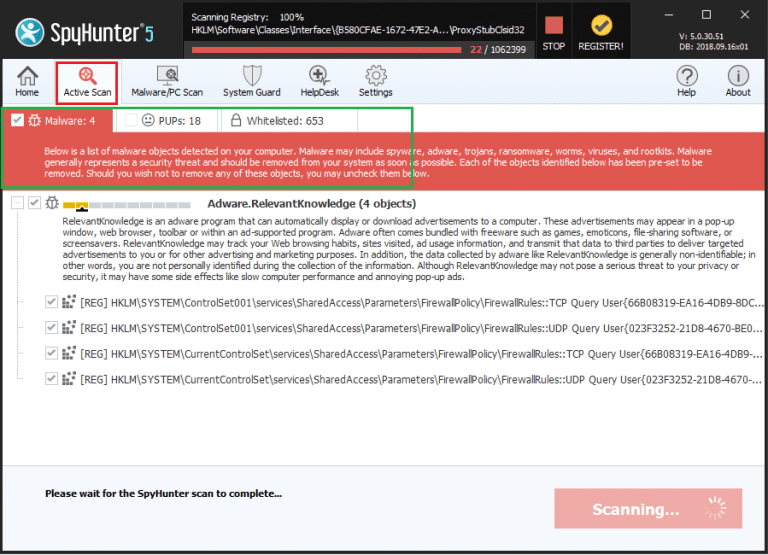
Wait for the few minutes to scan gets completed. On completion, it scan result report is presented on the screen.
⇒ Register for the Spyhunter and remove Controlhost.exe and all detected threats
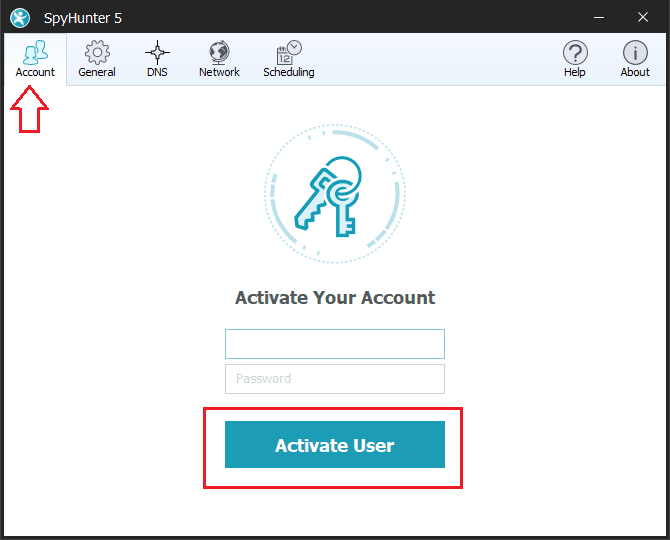
To delete Controlhost.exe and all associated threats found through the system scan, you need to register for the SpyHunter:
- Click on the register button available on the top-right corner of the program window,and then click on buy button.
- You will automatically be redirected to the purchasing page, enter your customer detail and valid email address,
- After the successful payment, you will receive email confirmation message. The email contains the account information such as usernames and passwords and so on,
- Thereafter, enter the same detail in the Account tab of the settings section of the program. Now, you can avail full features and protection to your system.
⇒ Steps to remove Controlhost.exe and other detected threats:
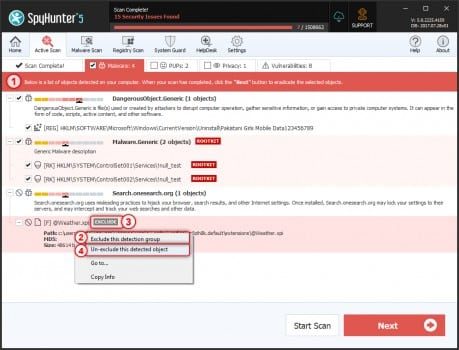
Spyhunter antivirus tool categorizes the type of objects detected during system scans in total five sections – “Malware“, “PUPs” (Potentially Unwanted Programs), “Privacy“, “Vulnerabilities“, and “Whitelisted objects“
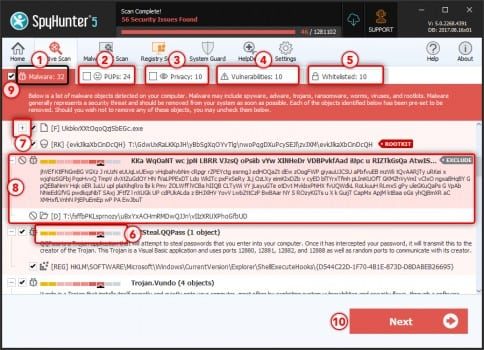
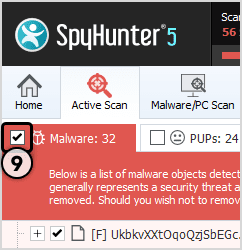
Select the object you want to remove and then click on Next button (you can quarantine an object so that you can anytime restore it to the system using restore feature)
Special Offer (For Windows)
Controlhost.exe can re-install itself if its associated files remain on system somehow. We suggest users to try Spyhunter to check and clean their system against all malicious files completely.
For more information, read SpyHunter’s EULA, Threat Assessment Criteria, and Privacy Policy. Spyhunter checks that your computer has malware with its free trial version. If found any threat, it takes 48 hours time for its removal. If you need to eliminate Controlhost.exe instantly, you are required to purchase licensed version of this software.