What does HPDM.framework / HPDeviceMonitoring.framework / HP Scanner 3 / HP Utility will damage your computer pop-up Alert means? Depth Analysis
- What does HP scanner 3 will damage your computer mean?
- How do you get rid of HP device monitoring framework will damage your computer?
- What does HP device monitoring framework will damage your computer mean?
- Is HP scanner 3 malware?
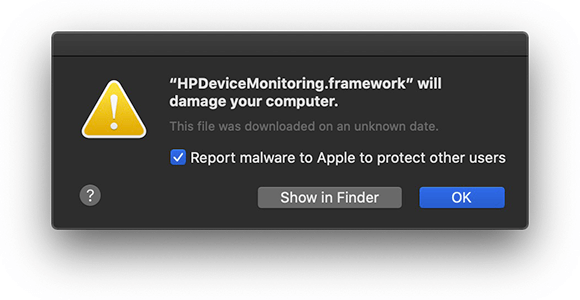
If you use Hewlett Packard printer with your Mac OS X work-station, you may come across a pop-ups similar to HPDM.framework / HPDeviceMonitoring.framework / HP Scanner 3 or HP Utility will damage your computer. This could create panic as suddenly the Mac OS starts considering HP drivers as malicious. Whenever you try to print any page, the alert message appears as:
“HPDeviceMonitoring.framework will damage your computer”. “The File was downloaded on an unknown date”.
If you think that HPDeviceMonitoring.framework is malicious then must know that it is not. It is a genuine component of HP software that ensures that compatible hardware easily communicates. It helps in getting regular updates and other technical assistance from the manufacturer’s server. The legitimate entity such as HPDeviceMonitoring.framework should not be flagged by Mac OS X but sometime it does.
What exactly HPDM.framework / HPDeviceMonitoring.framework / HP Scanner 3 / HP Utility will damage your computer Mac OS X means?
You are probably noticing this alert due to the Mac OS X security feature named as “GateKeeper”. Whenever Mac OS considers some unusual or potentially damaging code tries to get executed, it blocks the process and flags it through alert or pop-ups. This Mac OS security inspection is an automatic process and it immediately triggers the alert as soon as the users tries to run a doubtful application that may have unknown signatures or doubtful behaviors. This sounds excellent as far as PC security is concerned. However, the problems occur when the genuine process such as HPDM.framework or HPDeviceMonitoring.framework is red flagged by Mac security “Gatekeeper”.
According to HP representatives, they have intentionally revoked signatures or credentials on some old versions of Mac drivers. Many printer drivers are rendering code-signing certificates as void and null. So, when “GateKeeper” notices a missing certificate and invalid HP driver signatures, it blocks the software process and delivers alerts such as HPDeviceMonitoring.framework will damage your computer and so on. Some of the other similar pop-ups that you may notice are as follow:
- “inkjet3.driver” will damage your computer
- “Matterhorn.framework” will damage your computer
- “hpPostScriptpde.plugin” will damage your computer
- “inkjet1.driver” will damage your computer
- “PDE.plugin will damage your computer
- “Productimprovementstudy.hptask” will damage your computer
- “ScanEventHandler.app” will damage your computer.
- “commandtohp.filter” will damage your computer
- “HPDeviceMonitoring.framework” will damage your computer
- “HPDM.framework” will damage your computer
- “hpPostProcessing.bundle” will damage your computer
- “FaxArchive.task” will damage your computer
- “Fax.Backend” will damage your computer
- “HP Scanner 3” will damage your computer
- “HP Utility” will damage your computer
Other Possible Reasons for HPDM.framework / HPDeviceMonitoring.framework / HP Scanner 3 / HP Utility will damage your computer Mac Alert or Pop-up
On many occasion, the problem with the HP printer drivers due to the malware attacks. The cyber-criminals exploit the vulnerabilities in vendor’s websites in order to embed harmful scripts secretly. On thus they may get access to app released on the website (in this case, it will be HP drivers) and additional malware scripts hidden with it.
Though Mac OS X is considered to be safe from malware attacks as compared to Windows OS. However attacks on Mac is increasingly rapidly and is responsible for irritating alerts and pop-ups message and other severe issues related to browsing and data theft. It is recommended that you scan the work-station with a powerful anti-malware tool in order to fix continuous annoying printer problems.
Fix HPDM.framework / HPDeviceMonitoring.framework / HP Scanner 3 / HP Utility will damage your computer pop-up Issue in Non-Malware Attack Scenario
HPDM.framework / HPDeviceMonitoring.framework pop-ups occur when “GateKeeper” finds misconfiguration such as invalid code-signing certificate and so on. Though this Mac security feature alerts you regarding the problem, it doesn’t provide any solution. So, to fix the issue, you may try the below mentioned steps.
- Use AirPrint: This feature is supported by many of the printer where no printer driver is required to print. On other case, you have to continue executing other trial and error methods mentioned below.
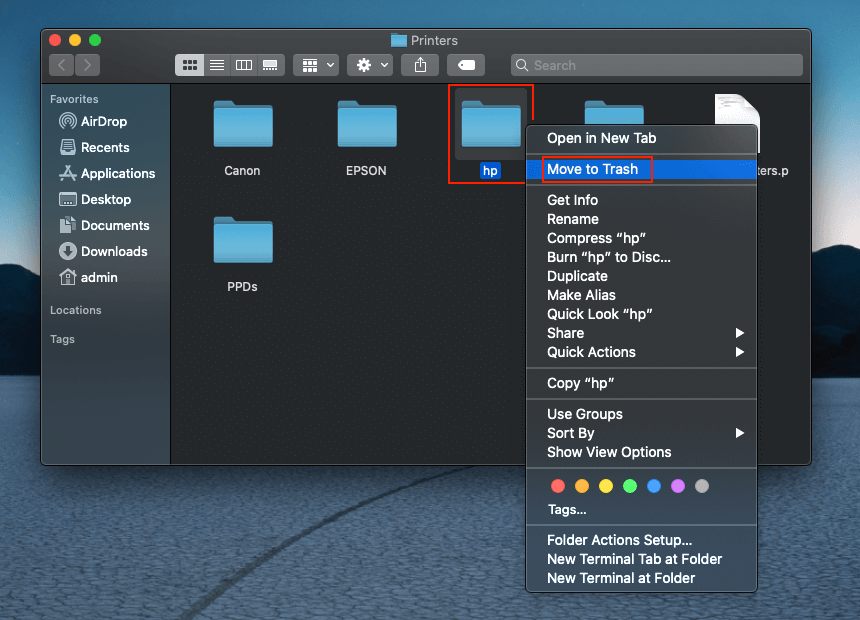
- Delete the Faulty Drivers: Go to Library/Printers and move “HP” folder to trash. Go to “System Preferences > Printers and Scanners” and delete the HP printer.
- Install the Right Driver: Once the above step gets completed, reconnect the printer through USB port. The Mac OS X will automatically offer you to download and install the most compatible software. In few minutes, the process will get completed.
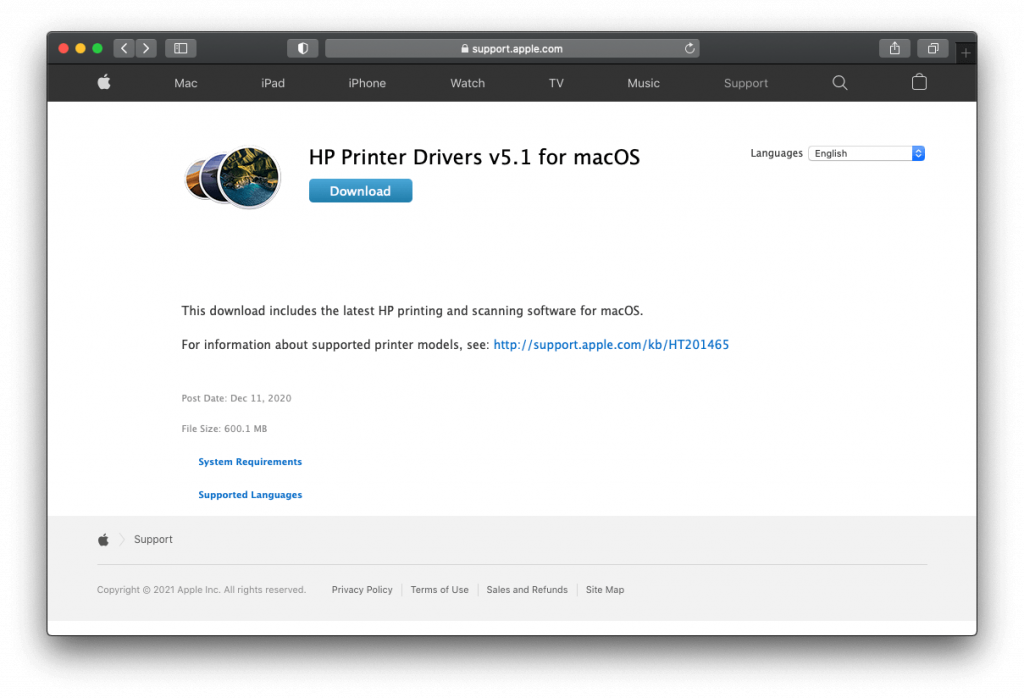
- Download Driver Manually: In case if the System doesn’t detect the driver automatically, you have to download it manually. Visit support.hp.com and search for the printer driver based on your printer model. In case if you are using HP printer manufactured before 2017, visit support.apple.com to install “HP Printer Driver v5.1 for Mac OS X package.
If the above mentioned steps work then it is best. However, if the problem is due to malware activity on your Mac OS X, you have to follow the below steps. The proper guide for malware intrusion, its removal including manual as well as automatic process has been discussed below.
〈How malware can infect Mac OS X based PC?〉
Spam Emails:
The targeted potential victims are tricked to downloaded harmful files. You may receive a mail with an attached file claiming that it is a delivery receipt, invoice or tax refund documents. It may say to open the attached file to get items delivered to you or to get money. Simply, opening the attached file will end up installing malware. Such spam emails usually have spelling or grammatical errors. They may asks you to update your personal details and provide a link to do so.
Bundled with Other Software (Bundling)
In many cases, the users face issues right after they have installed any program in the work-station. This directly means that some malware can get installed along with any other software. This includes application from third-party platforms and peer-to-peer file sharing networks. They can download an extra toolbar or extension categorized as PUPs and their only aim is to show excessive ads and pop-ups. In researches, it got notice that the program that generates software keys (keygens) often install other doubtful application along with them. It is important that you carefully read with you are installing. Download any software only from a trusted source.
Through Hacked Webpages
If there is software vulnerability then this can be utilized by the Malware to infect your PC. If you visit any malicious websites, such loopholes can easily be installed to download harmful files without your knowledge. Hence you should always get the latest updates for the software you use.
Infected Removable Drives
Originally, the most popular way to insert malware was through any external storage device. Recently, the firmware of a USB stick is used to doing the same. The malware are hidden under the firmware and it is very difficult to detect. Additionally, a USB, external hard-disk or drives, CDs, DVDs etc. may contain unsafe files attached to them.
Not Using Internet Security Program or Anti-malware Tool
Even today in this digital world, there are many users who don’t understand the importance of PC security software. It is very important to have a proper protection for all your devices. The business in the malware world is booming and you could definitely be their next victim if you are not careful. As an tech savvy individual, you know exactly what to look for as far as malware infection is concerned but knowing that you can even get infected with malware even when you visit a compromised website. It is extremely important to have a proper Internet security program or anti-malware application in the work-station.
〈Why MacKeeper?〉
If you are unaware, we tell you that your device has built-in antivirus tool already installed on your system to protect the system from PC threats and viruses. So, in such a case there is no need of any third party antivirus tool. However, using MacKeeper and other such tools become necessary because some PUAs like infection can easily bypass the built-in security and install on the system. After the installation, they disable the firewall alerts and make the completely vulnerable for other malicious malware infection. The default AV tools could not detect the entry because a lot of investment is done by crooks in making such applications appear legitimate upon detection.
MacKeeper is helpful in this case. It is especially tuned up for protecting the system from any potentially unwanted applications. Also, it can check the system for other potentially dangerous malware like Trojan, Ransomware, worm and so on. Hence, it will ensure that these threats could not lead personal data leakage. Not only that, it will tune up the performance of the system by removing junk, duplicates and useless applications, Mac’s memory and log-ins items and so on.
MacKeeper: Download/ installation guide
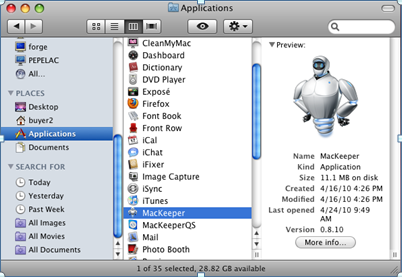
- Click on here to download MacKeeper file within the system,
- When the installation process is completed, a file named MacKeeper.dmg or MacKeeper.pkg will be downloaded within the system,
- Go to the Finder and Select Downloads to see this file,
- Then, open it to begin installation process and follow the on-screen instructions to finish the process.
Use the program’s free/ paid version
MacKeeper has certain features that the users can try once for free to see how it works. However, the app’s features will not work until you purchase the license version. So, purchase the full license version of the program if you want to keep all the benefits of the app.
Steps to find activation code:
- Open the program,
- Click on green unlock Full version in the bottom-left corner of the page,
- Then choose your Plan
Once the purchasing is proceeded, you will get the 16- digit activation code on the screen. This code will also be sent to the email address you provided. When you have the Activation key, follow the below steps to get access to the full features of the app:
- Open the program,
- Click MacKeeper and choose Enter Activation Code,
- Paste the activation code in the MacKeeper Window and then click Apply
In the process, you will be asked for the Mackeeper account. If you don’t have, create one. If have, log-in in to this and complete the activation process.

MacKeeper setup guide:
- Open the program and click on Start Full Scan,
- Then, select Fix Items Safely option,
- Follow the setup prompts next to this,
- Click on Done option when all suggestions are completed.
This is the required steps to complete the MacKeeper setup. Next, launch the scan and check for system for malware and all its malicious components for their removal.
User guide to remove malware using MacKeeper:
- Open MacKeeper,
- Select Antivirus on the left sidebar, and then click on Launch Antivirus,
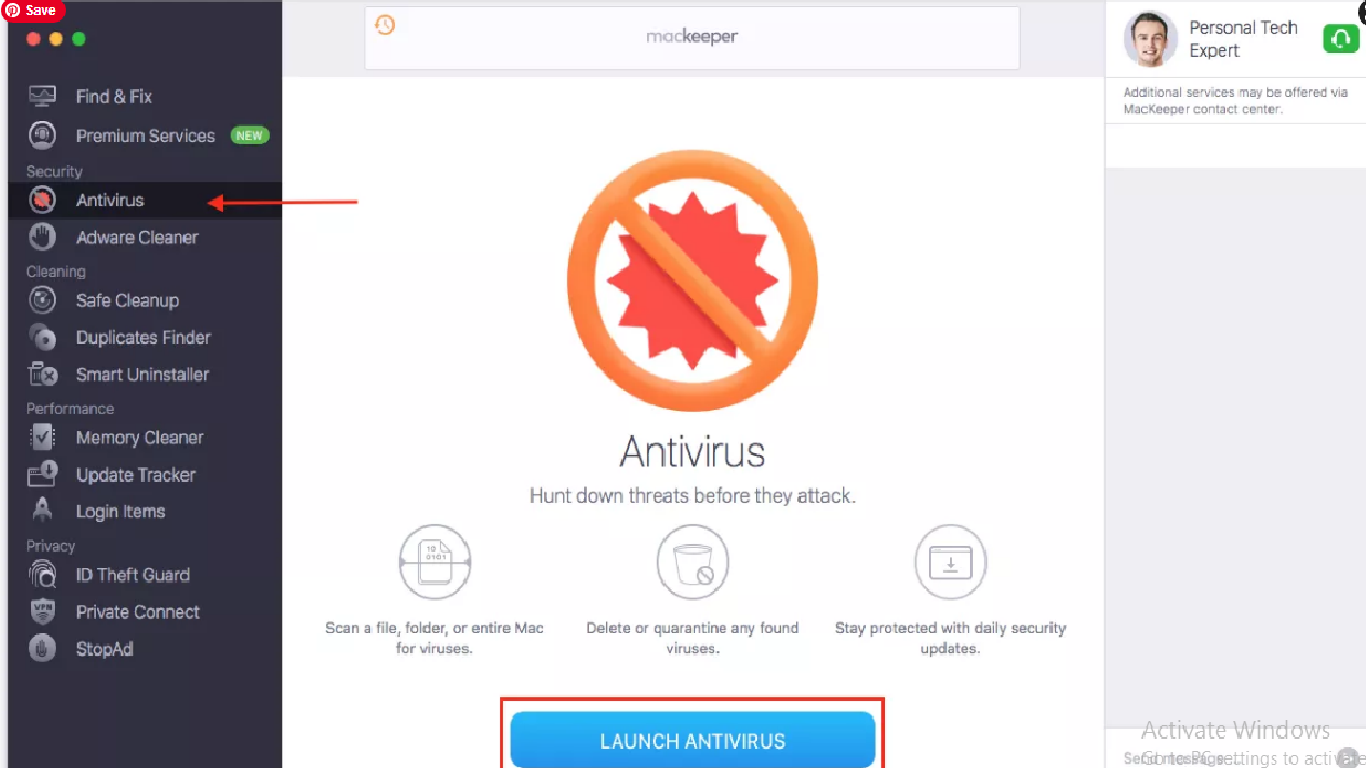
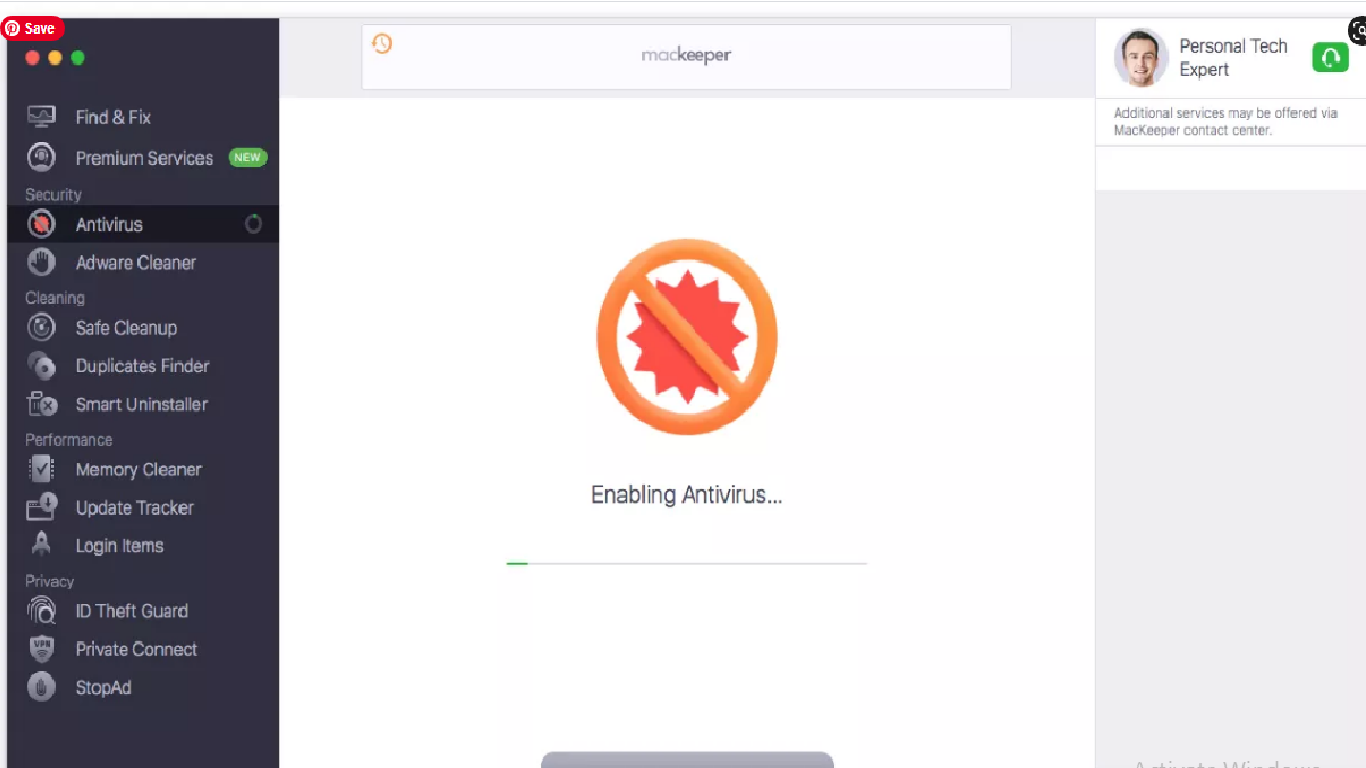
- Antivirus will start enabling (the process takes few seconds to start),
- Click on Custom Scan to check for specific folder or USD drive,
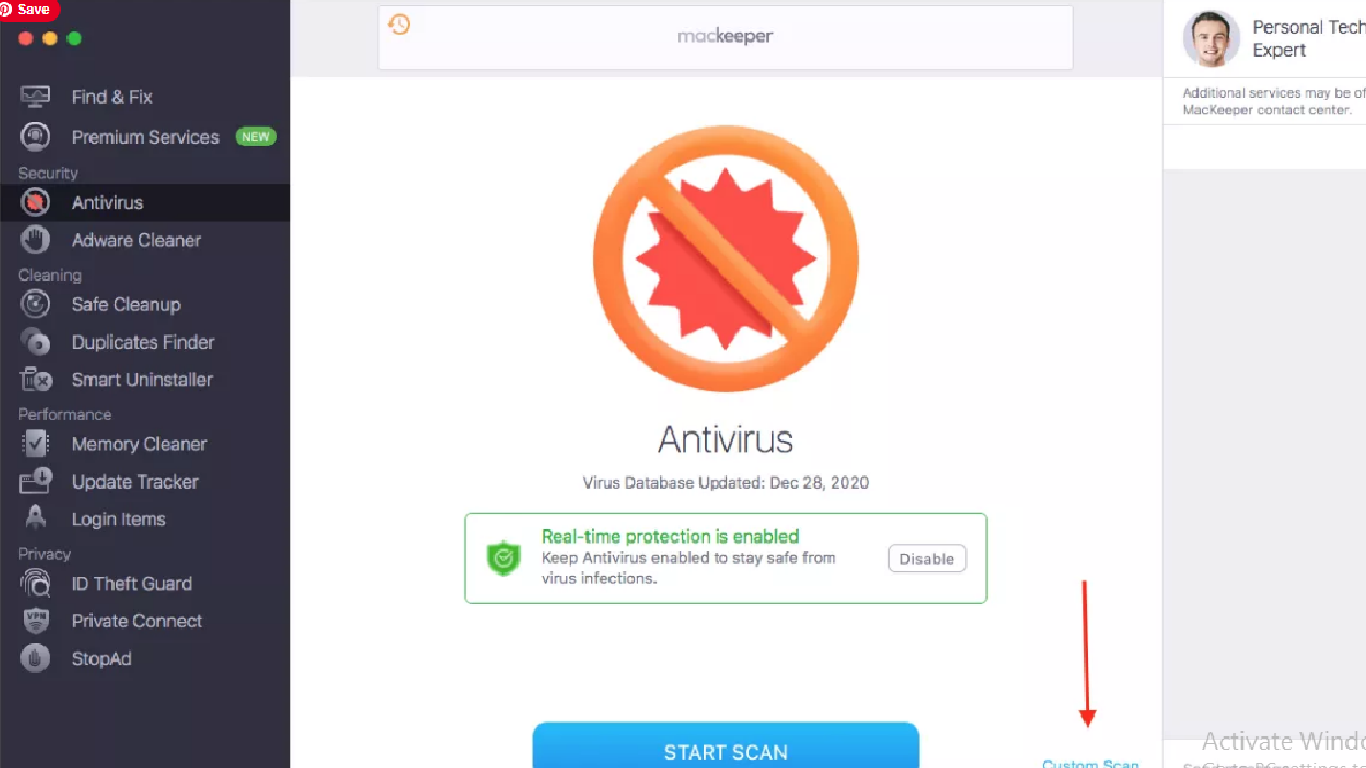
The software scans for all viruses, malware, Trojans and other major threats on the system and when the process is complete, it shows the result on the screen. If your Mac is safe, you will see the following screen:
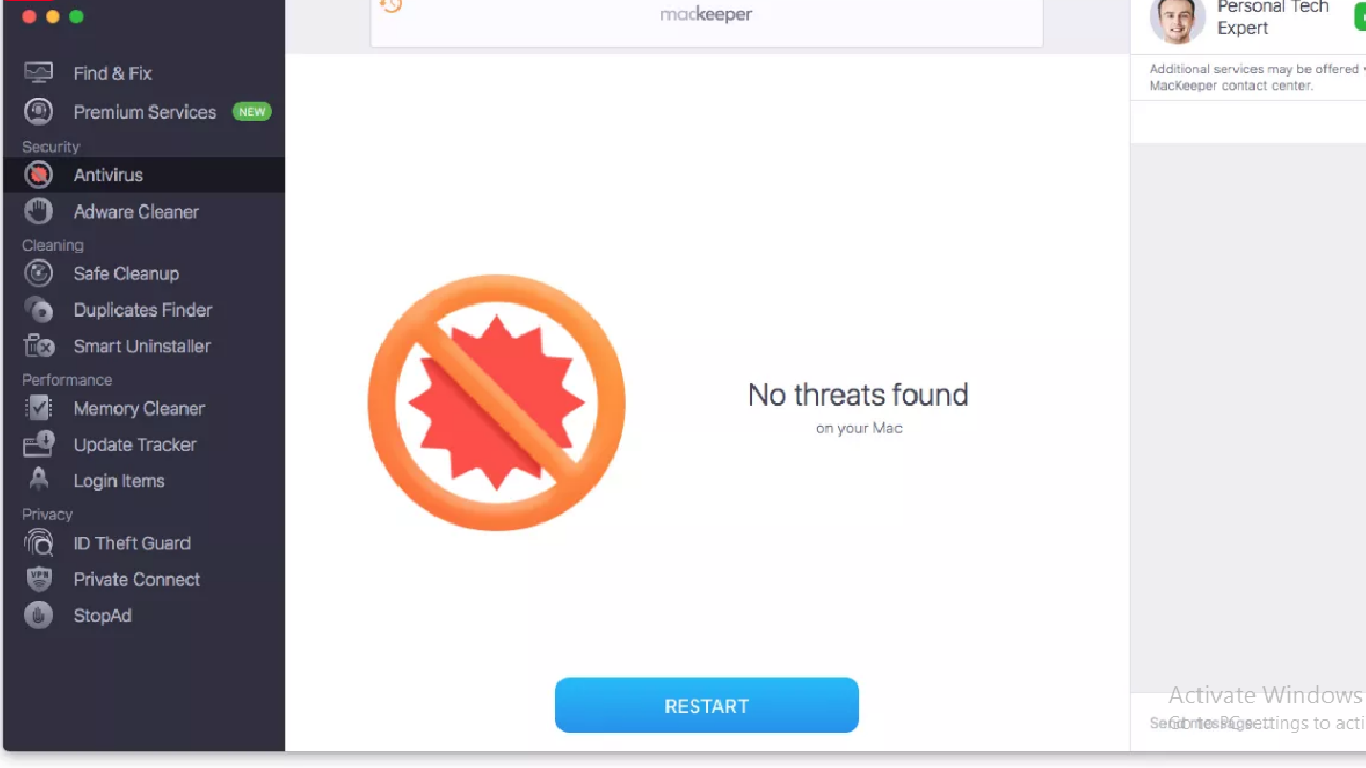
However, if the scanning result shows any malicious detection, click on the items that are malicious and remove those by clicking delete button (or you can Quarantine to isolate them from infecting the device).
Next to this, choose malware Cleaner option in Antivirus Section, and click Open (the software will then scan the system for malware, browser hijacker and other potentially unwanted applications):
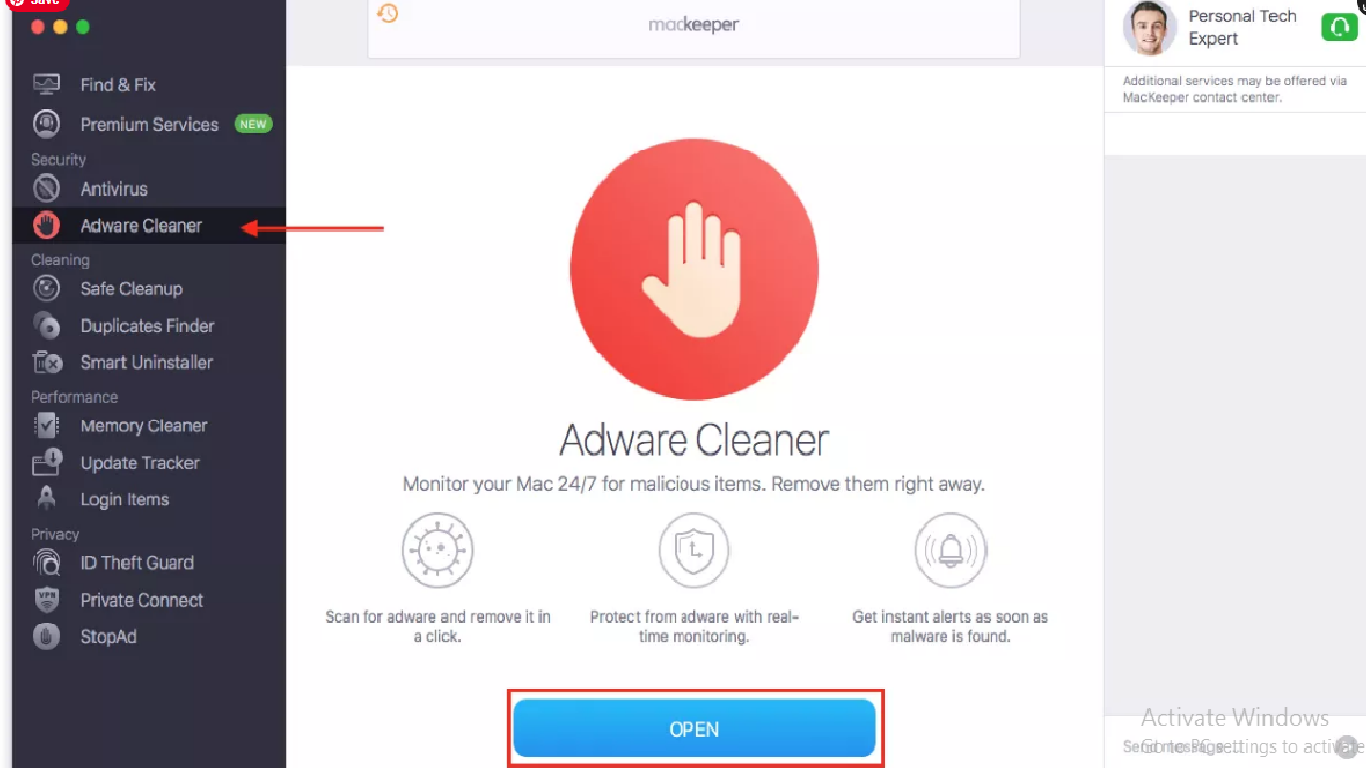
- click on Start Scan button,
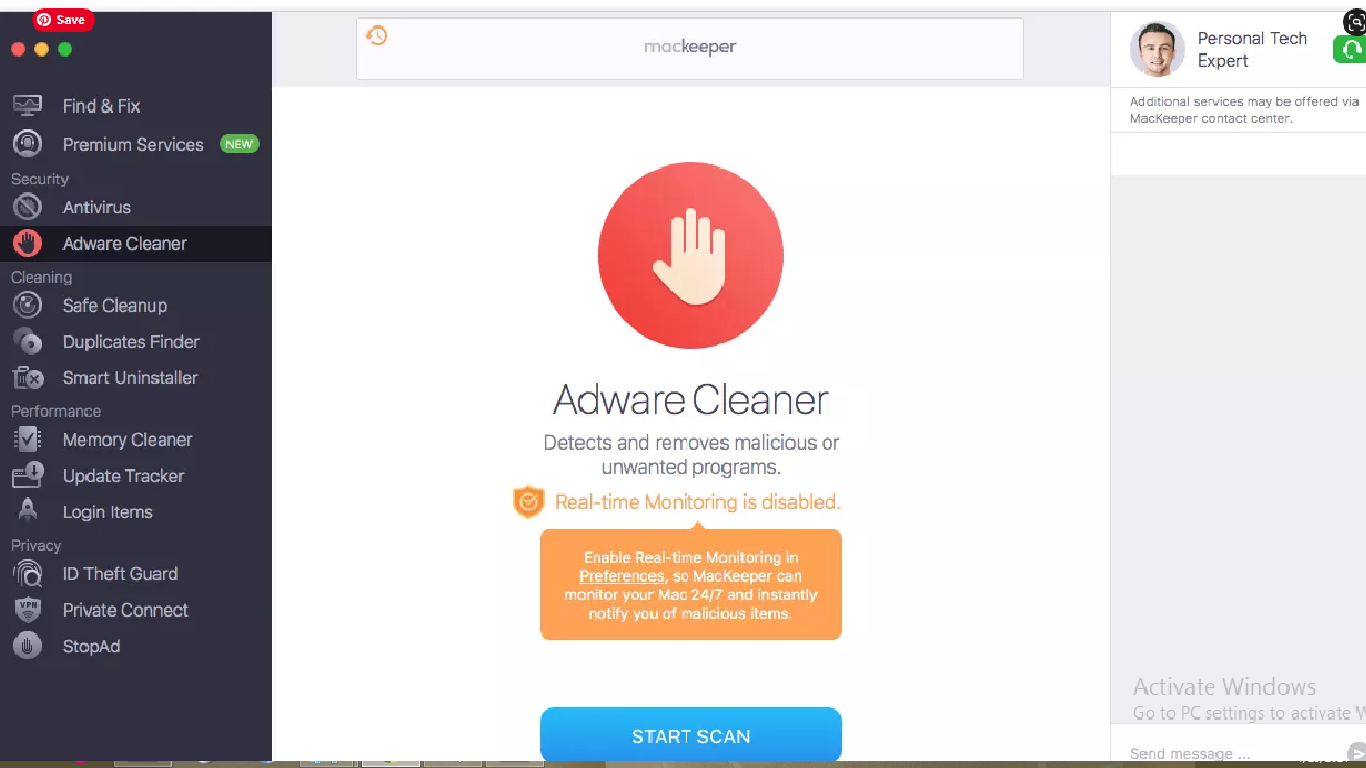
- Once scanning process is completed, the program shows the scan results on the screen. Take the immediate actions.
Special Offer (Macintosh)
Mac users if infected by malware, can try a suggested application to do scan and check if all malicious files and entries are completely removed.
〈Remove malware using the following steps:〉
⇒ Delete malware from MacOS X
⇒ Erase malware from Google Chrome
⇒ Remove malware from Mozilla Firefox
⇒ Delete malware from Safari
→ Get rid of malware from Mac OS system
To completely un-install malware, you need to delete all its related components by the steps below:
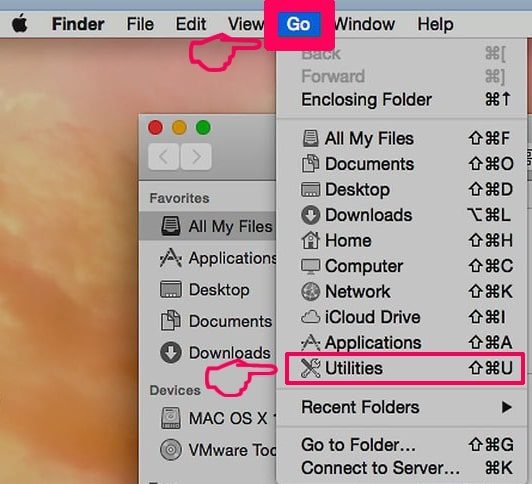
- Click on Go> utilities,
- Double-click on the Activity Monitor,

- Check for malware related processes in the opened window,
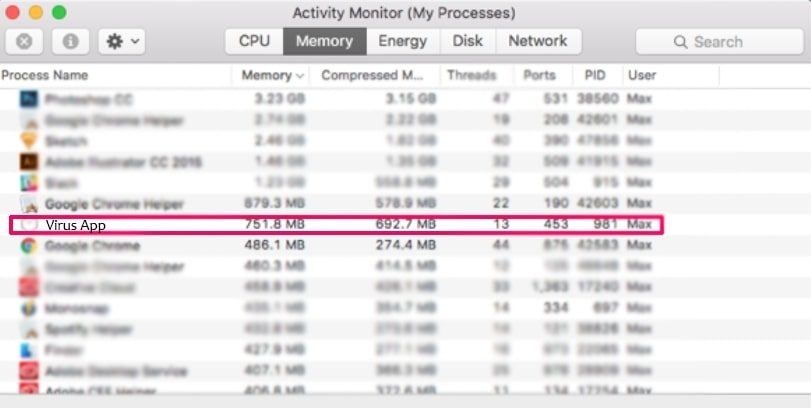
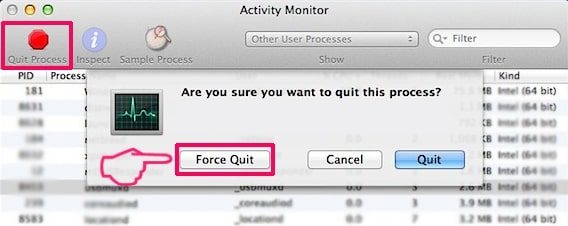
- Forcibly quit these process by clicking Force Quit option
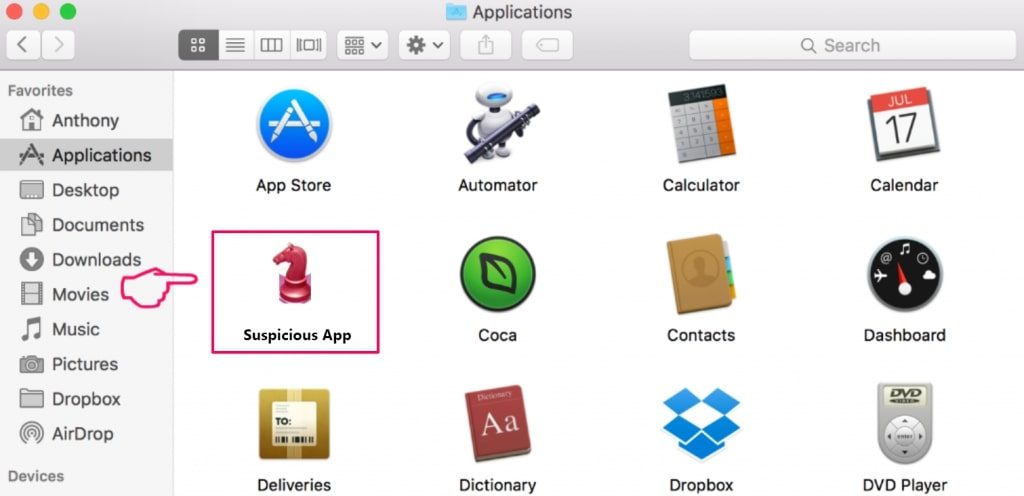
- Then, click on Go> Applications to open Applications Menu,
- Under this menu, look all suspicious files or apps with name identical to malware and move all of them to trash by clicking right-click and selecting Move To Trash option,
- Next to this, select your account and click on Log-in items preference.
A page appears with a list of the apps that automatically start with your log-in. Check for the suspicious malware files and stop them to run automatically by clicking “Minus” icon next to it.
Now, look for the left-over files by the following sub-steps:
- Click on Finder and search with the name you want to remove on the search bar,
- Change the drop down menus with “System Files” and “Are Included” (by this, you will be able to see all associated files with the application you want to remove. The list might include some files which are not related to the app and be careful about it),
- Then, make selection to the files and drive then to Trash
In case, you can’t find malware and related files and objects in your Applications or other places as shown above, you should check the system on Libraries:
- Click Go> Go To Folder,
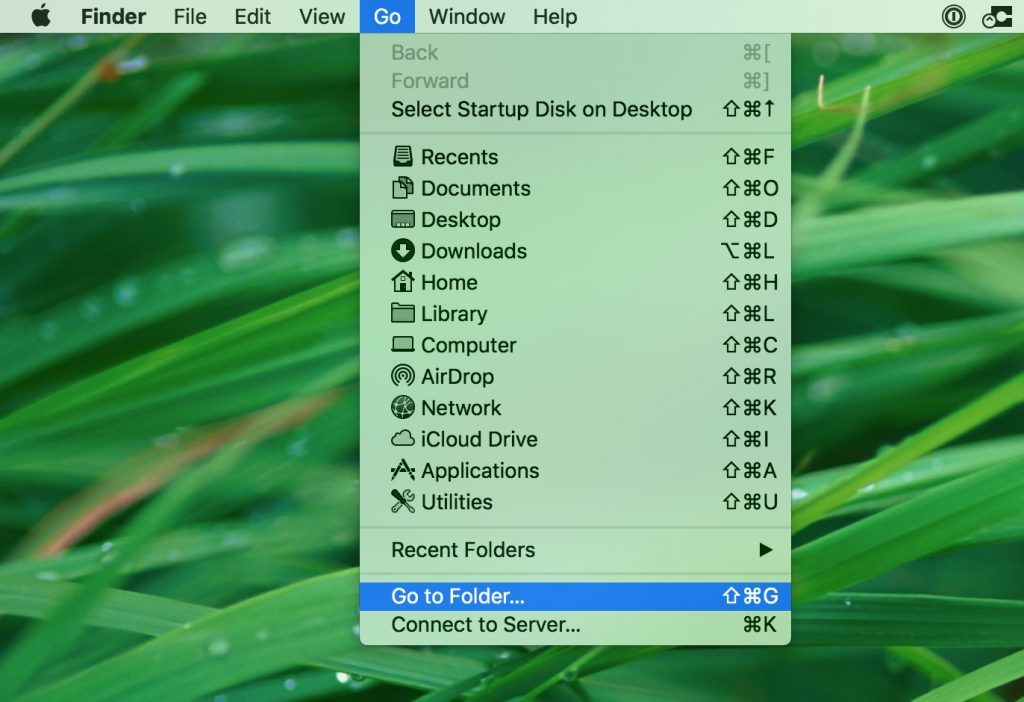
- Type “/Library/LauchAgents/” and press Ok,
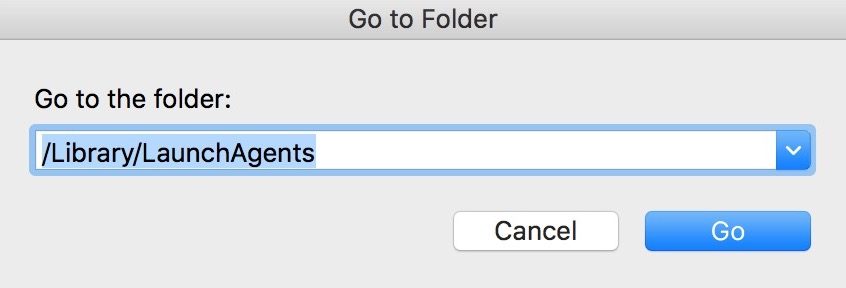
- Delete all the files related to malware. Do not delete any such files that you think not associated with the virus.
- Repeat the same process to check for malware related components in other Library directories:
→ ~/Library/LaunchAgents
/Library/LaunchDaemons
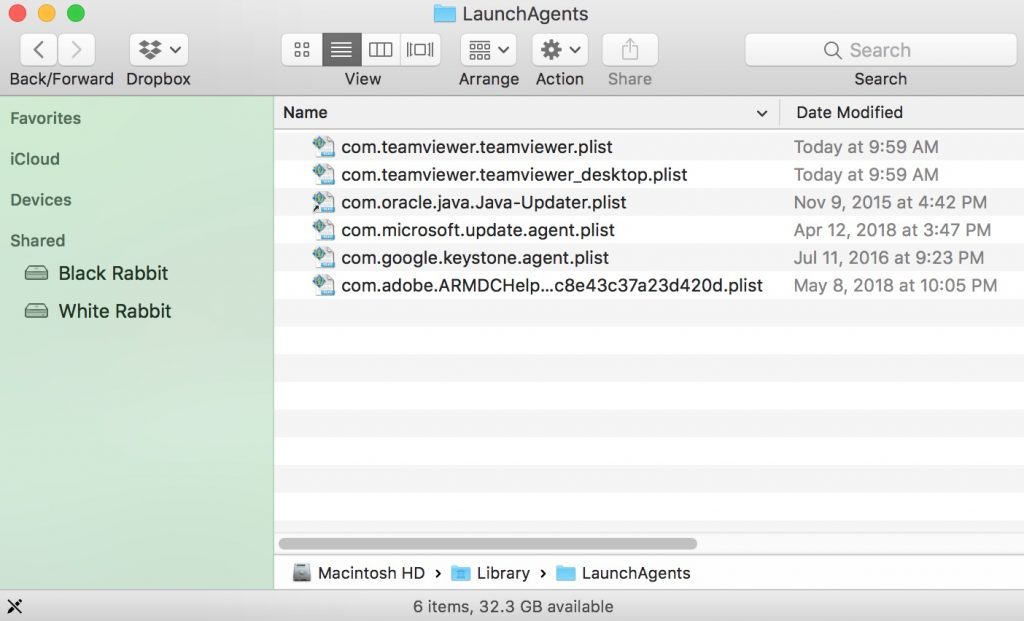
→ Erase malware from Google Chrome
Delete malicious extensions:
- Open the Google Chrome and click on the drop menu,
- Move the cursor over More Tools and select Extensions,
- In the newly opened window, check for all suspicious plug-ins related to malware and remove them by clicking Remove button.
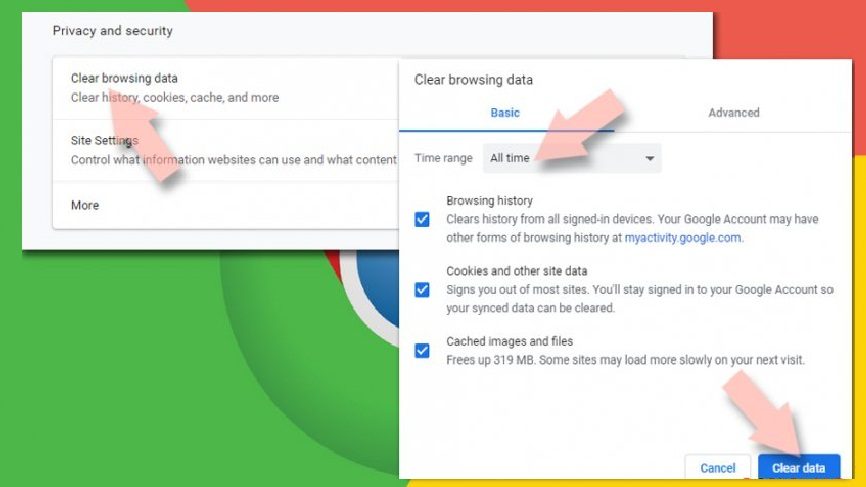
Clear the browser cache and web data:
- Click on Menu,
- Select Settings,
- Under the privacy and security, select the option says Clear browsing data,
- Click on Browsing history, Cookies and other site data and also the Cached image and files to make selection,
- Then, delete the selected items by clicking the Clear data
Restore the browsers’ homepage:
- Click on Menu and choose Settings,
- In the On Startup section, look for the suspicious malware site,
- Then, click on Open a specific or set of pages, select three dots and click on Remove
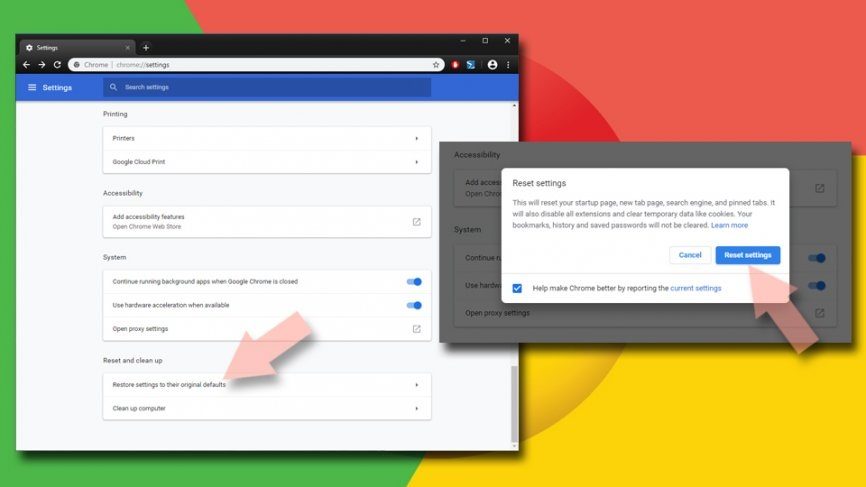
Reset Google Chrome:
Completely reset the web browser to automatically remove all suspicious elements associated with malware:
- Click on Menu and go to the Settings,
- Click Advanced,
- Scroll down to find Reset and clean up,
- In this section, click on Restore settings to their original defaults,
- And finally, confirm with clicking on Reset settings.
→ Remove malware from Mozilla Firefox
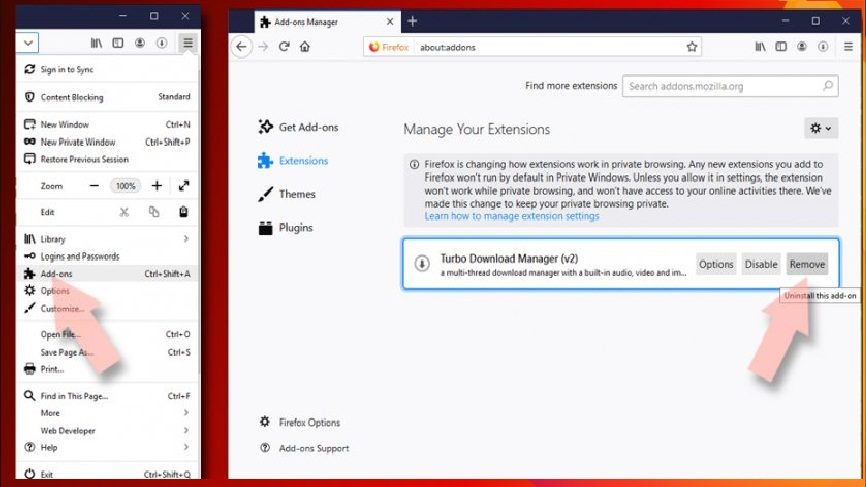
Remove malicious extensions:
- Open Firefox and click on Menu (by clicking three horizontal lines at the top right of the page),
- Select Add-ons, select all plug-ins related to malware and remove them
Change the homepage:
- Go to the Menu and choose Options,
- Under the Home option, enter the preferred site that you want to open each time when you newly open the web browser
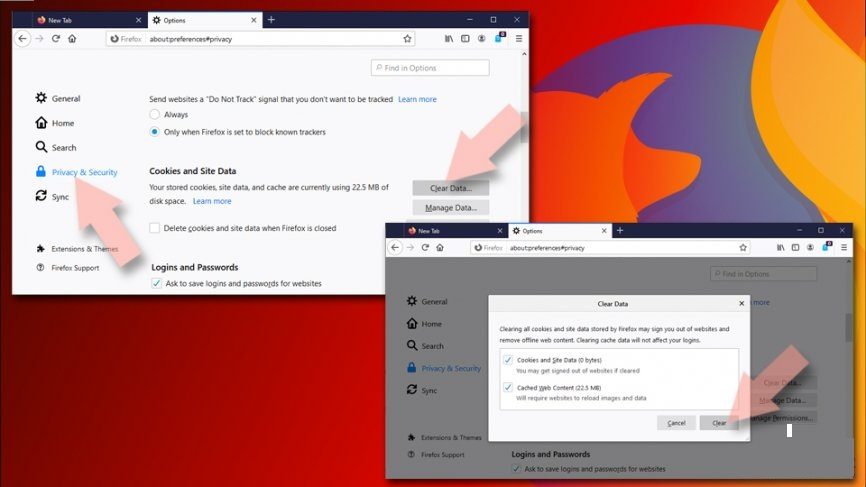
Clear cookies and site data:
- Click on Menu and choose Options,
- Under the Privacy and Security, find cookies and Site Data,
- Click on Clear Data,
- Select Cookies and Site Data and also the Cached web content and then click
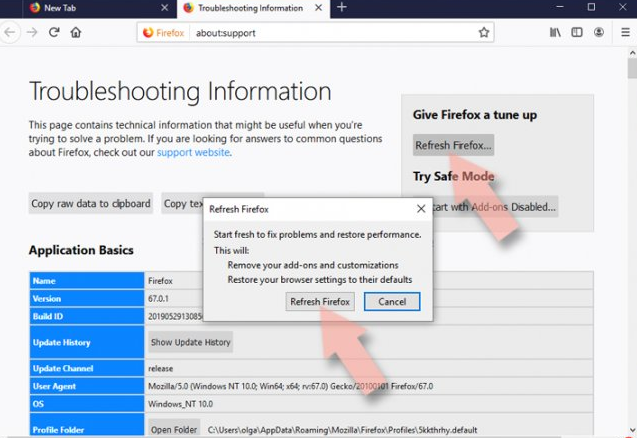
Reset Firefox:
- Open the web browser and click on Menu,
- Go to Help section and find Troubleshooting information,
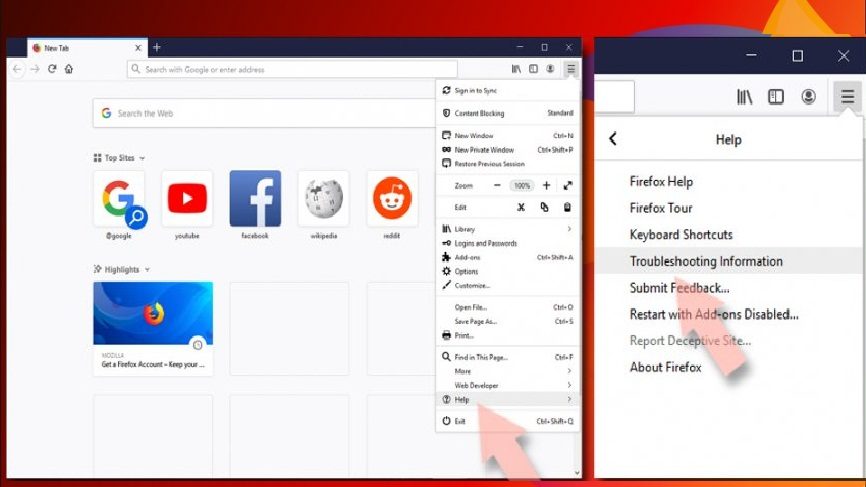
- Click on Refresh Firefox… under the Give Firefox a tune up section,
- Then, you will have a pop-up shows to the screen, confirm with clicking on Refresh Firefox to complete the process.
→ Delete malware from Safari
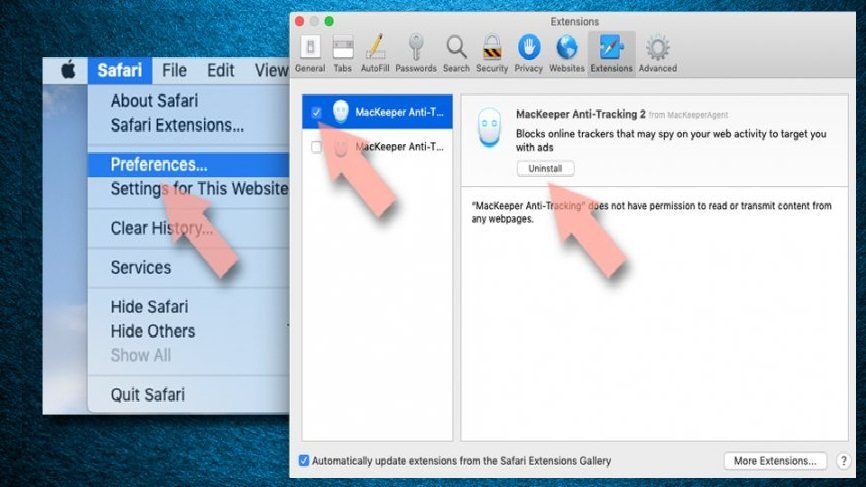
Remove unwanted extensions:
- Click on Safari and go to preferences,
- Pick Extensions in the opened window,
- Then, select the unwanted extensions related to malware and click on Un-install.
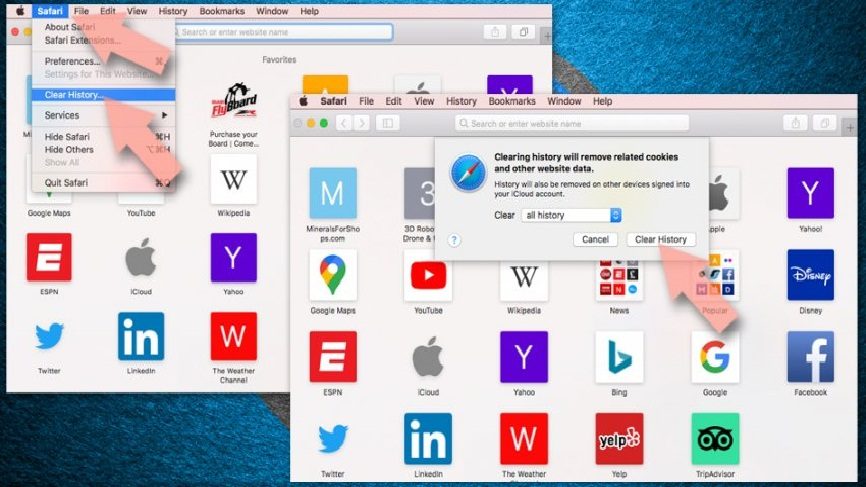
Clear cookies and other website data:
- Go to the Clear History option under Safari,
- In the Clear section, pick all history,
- And Confirm with Clear History.
Reset Safari:
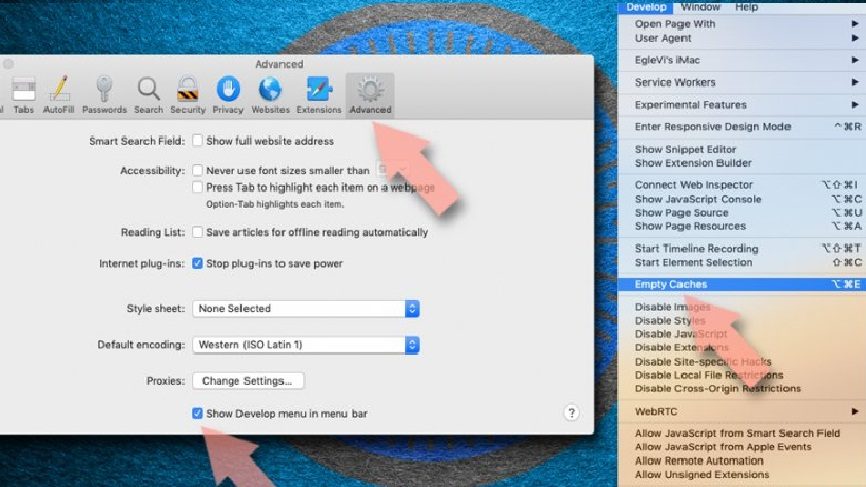
- Go to the Preferences by clicking Safari> Preferences,
- Click on Advanced tab,
- Select Show Develop menu,
- Click Develop and then select Empty Caches
After completing these steps to remove malware and associated components from all web browsers installed, you should run a full system scan using some reputable antivirus tool that will help you in getting rid of all the registry traces for the infection and deleting other possible malware that may possible infiltrate system during the time interval you are dealing with system infection on your computer.
Up till now, you have seen how you can manually get rid of malware infection. As you have seen, you have to go through to every possible section on your system such as Applications, Library and to the installed web browsers for suspicious components related to the malicious malware. If you belong to a highly experienced user, you might have no problem in using this manual approach for the malware removal.
However, when we consider the people who are beginner or the less tech savvy who have not much IT skills and have not deal with virus removal steps ever before, the manual malware removal tasks will be difficult for them. Especially for you, we are preparing the automatic malware removal guide. Below, you will see how you can find all suspicious applications on your system by system check using professional tool called “MacKeeper.” The users should use this approach, if they want the removal process to be done in quick and without any hassles. Before we go and understand how to use this software for system scan and remove the suspicious objects, let’s know a little about the software to know what makes software superior than all alternatives.
Special Offer (Macintosh)
Mac users if infected by malware, can try a suggested application to do scan and check if all malicious files and entries are completely removed.
Protect your system and privacy
There are multiple ways how you can protect yourself online. You can use incognito, however, you will be traced even in this mode for advertisements. There is a way to add a protection layer to and cerate complete anonymous web browsing experience using some VPN. These software provide private internet access, reroute through different servers by disguising the IP addresses and geo-locations. Also, these will ensure no data will get recorded, leakage and available to third parties as they follow strict no-log policy. This combination of a secure web browser and VPN will help you browse the internet without being targeted by third parties/ cybercriminals.